Alliance IT Blog
Love Is: Protection from Cyberattacks
This Valentine's Day, prove your love and loyalty to customers and users by protecting their data from cyberattacks.
7 Ways to Protect Customer Data
Protecting customer data is vital for many diverse reasons - ranging from goodwill and customer trust to protection from lawsuits.
How To Optimize Your IT Budget in 2024
By routinely reviewing and adjusting your IT expenses, you can ensure that your budget for technology is most aligned with your objectives.
5 Smart Tech Moves for 2024
Moving too impulsively in regard to new tech may inspire confusion and financial headaches; dragging one's proverbial feet can render companies behind the curve competitively.
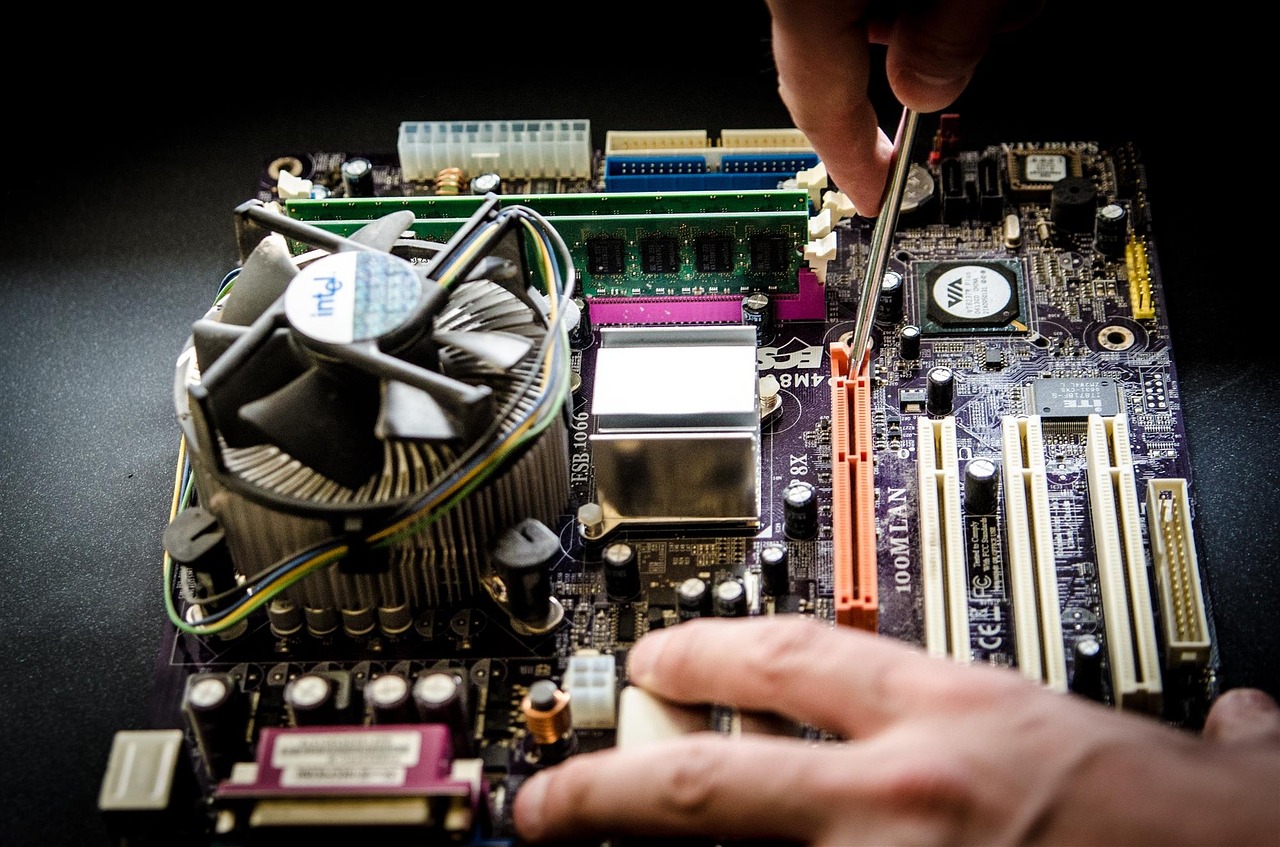
Comprehensive IT Assessments
Comprehensive information technology assessments match IT resources with software applications and expectations of essential stakeholders.
Elements of Targeted IT Assessments
Targeted IT assessments give the organization actionable solutions to daily issues and challenges across all core competencies.
Does Your Business Need VoIP?
Robust scalability is often the most significant benefit of VoIP for small businesses who need solutions to support their growth. .
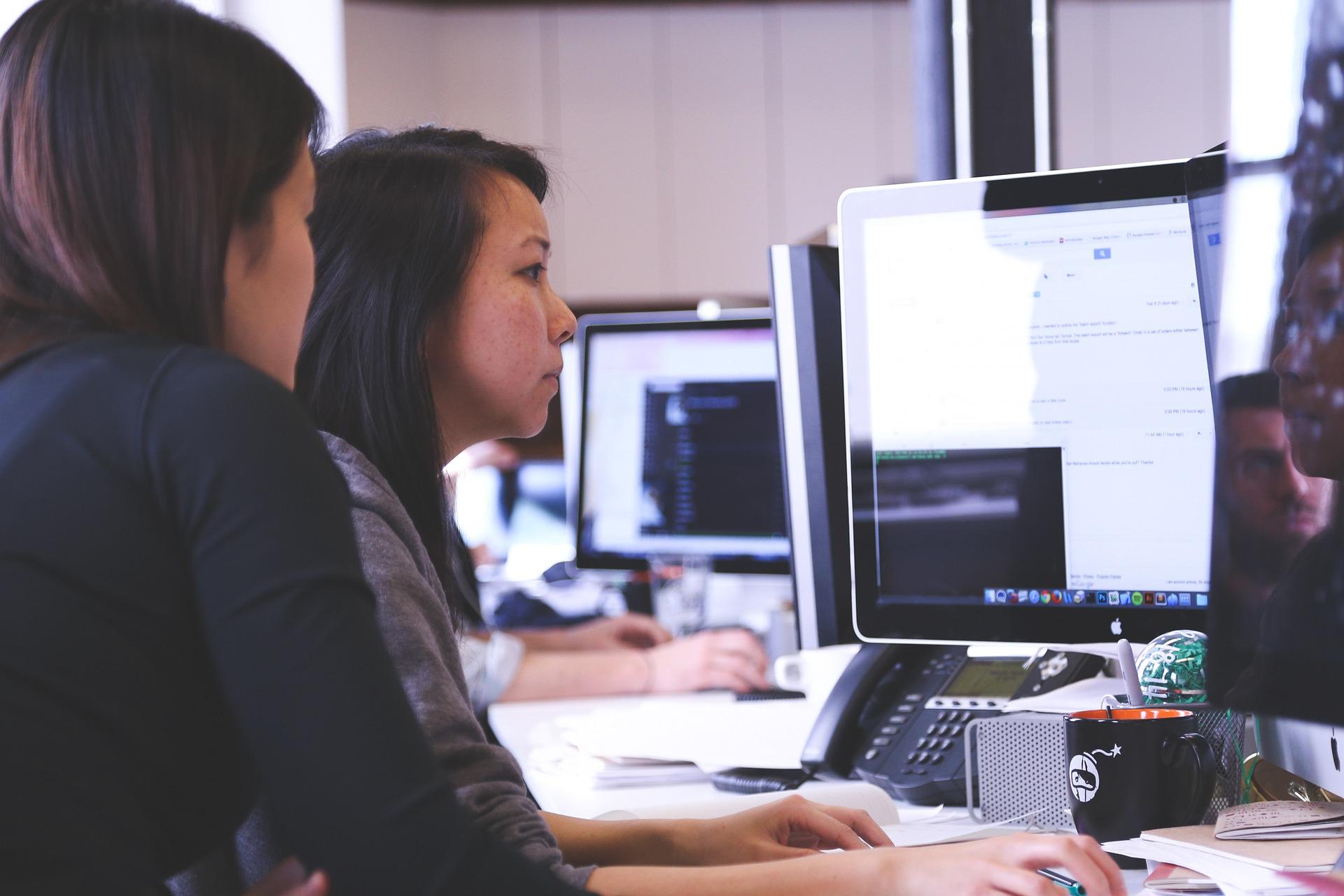
6 Ways MSPs Can Maximize Workplace Efficiency
Managed services improve operational efficiency by providing effective optimization of infrastructure and robust data protection.
IT Department Resolutions for 2024
With the right strategy and team in place, your IT department can ensure that 2024 is a fantastic year for efficiency and productivity.
7 Ways to Make Your Network More Productive in 2024
As we look forward to 2024, we examine best practices to maximize network performance and keep operations running as expected.
Managed IT Services in Review
Managed IT services guarantee access to professional experience in all emerging technology areas while protecting network integrity.
Spotlight: Managed Detection and Response
Managed detection and response (MDR) helps to understand the potential of cybersecurity threats and improve how to address those threats.